Monkey is a super cool program (ships along with Android SDK, hence you don’t have to do any installation) which does
stress testing of your application. It actually generates pseudo-random streams of user even like clicking, touching and making gestures along with some system level events like rotating phone, muting the phone, turning off data connection etc. Monkey will stress test your application in both emulators and in you real hardware device.
Execution
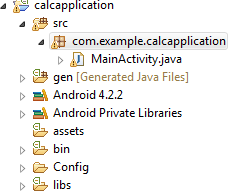
Monkey is a command-line tool, hence to execute the tool you have to do is first get the package name of your
apk file (The application under test).
In my case, I am going to test my calculator application (You want to download the application, here is
the link) and the name of the package is
com.example.calcapplication as shown below
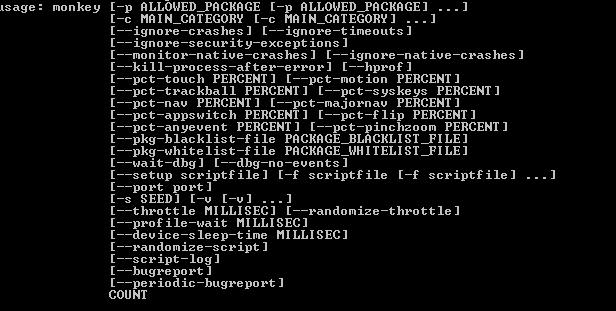
Now, here is the command to run Monkey from command prompt
adb shell monkey -p com.example.calcapplication -v 2000
As you could see, I have given
–p for package name which is followed by the package name of my application, similarly I have given
2000 which is the number of pseudo-random event I am going to execute against my application.
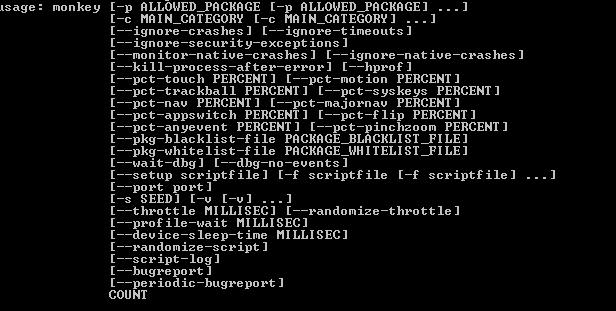
You can see the full list of command from here
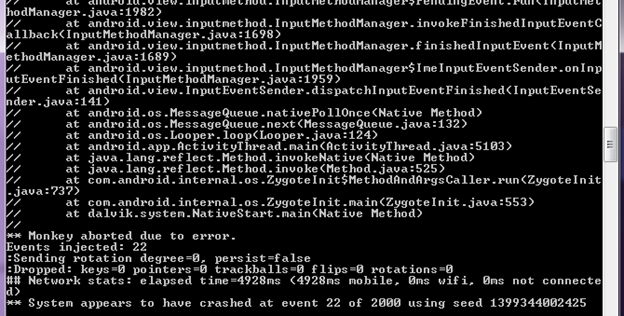
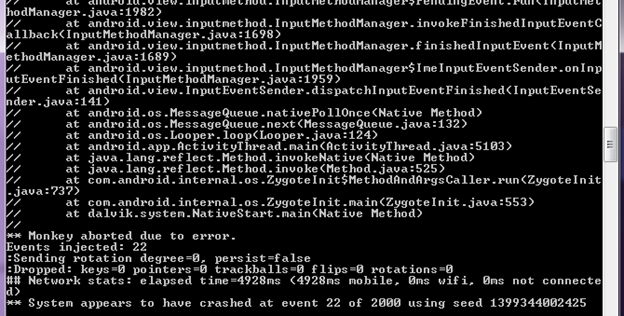
Let’s execute the above command against my application but the bad news is my application broken at
22nd event itself
L
Here is the screenshot
It’s really a very interesting tool to stress test your application and for testers it’s a very good tool to showcase your skill in stress testing of android applications too
J
Thanks,
Karthik KK
 Now, here is the command to run Monkey from command prompt
Now, here is the command to run Monkey from command prompt
 Let’s execute the above command against my application but the bad news is my application broken at 22nd event itself L
Here is the screenshot
Let’s execute the above command against my application but the bad news is my application broken at 22nd event itself L
Here is the screenshot
 It’s really a very interesting tool to stress test your application and for testers it’s a very good tool to showcase your skill in stress testing of android applications too J
Thanks,
Karthik KK
It’s really a very interesting tool to stress test your application and for testers it’s a very good tool to showcase your skill in stress testing of android applications too J
Thanks,
Karthik KK
Hello,
I’m trying to download the file link however is giving 404 error page, could make the file available again, I have great interest to see how the monkey but I am having great difficulty.
Note: sorry English because I am Brazilian and I do not know much English.
Here is one of the essayist way to run monkey with below shell script.
Shell Script for run monkey command in automated way it will generates all the necessary files such as Bug report, Video recording and screenshots and place them into respective device serial number specific folders.
https://github.com/ssirekumar/FourthMonkey